AWS Weekly Roundup: AWS Control Tower, Amazon Bedrock, Amazon OpenSearch Service, and More (October 9, 2023) | Amazon Web Services
As the Northern Hemisphere enjoys early fall and pumpkins take over the local farmers markets and…

As the Northern Hemisphere enjoys early fall and pumpkins take over the local farmers markets and…

In today’s digital age, where every idea wants its space on the internet, the value of…

Join us on Thursday, October 5, 2023, for a free-to-attend online event, Data and Generative AI…

Duncan is an award-winning editor with more than 20 years experience in journalism. Having launched his…

We launched the compute optimized Amazon EC2 C6a instances in February 2022 powered by 3rd Gen…
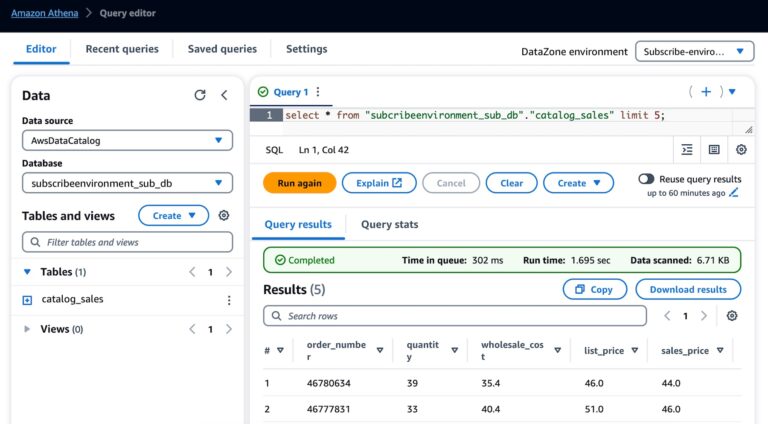
Today, we’re announcing the general availability of Amazon DataZone, a new data management service to catalog,…

For more than a decade, Rdiff-backup has been our preferred choice for developing Minarca Data Backup…
Satya Nadella, CEO of Microsoft: “We are on the cusp of a new era, where technology,…

Duncan is an award-winning editor with more than 20 years experience in journalism. Having launched his…

Introduction In the vast landscape of operating systems, Linux stands as a bastion of flexibility and…

James has more than a decade of experience as a tech journalist, writer and editor, and…

Insider security threats refer to cybersecurity threats that originate from within an organization. These threats can…

Last week I attended the AWS Summit Johannesburg. This was the first summit to be hosted…


Introduction Creating a bootable USB drive is a cornerstone skill for anyone interested in exploring different…
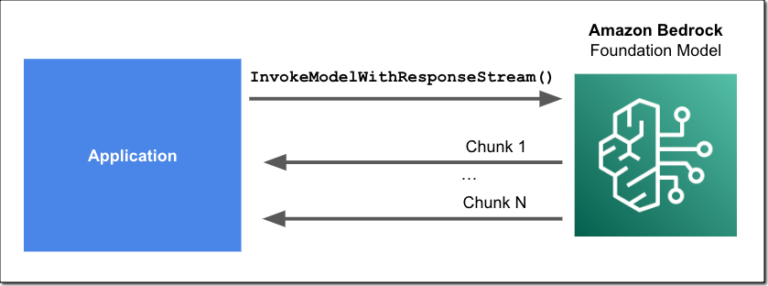
This April, we announced Amazon Bedrock as part of a set of new tools for building…
Threat hunting is a proactive cybersecurity process where specialists, known as threat hunters, search through networks…
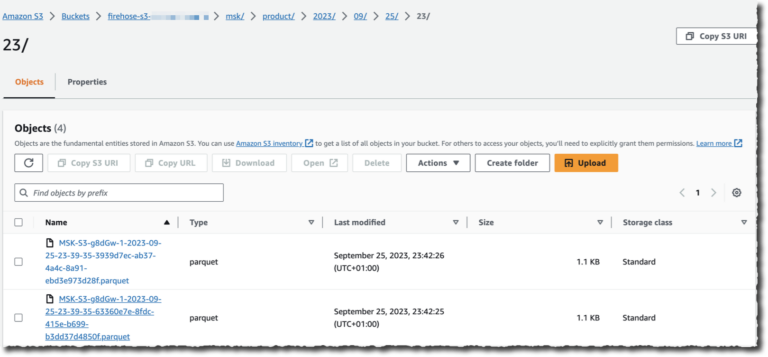
I’m excited to announce today a new capability of Amazon Managed Streaming for Apache Kafka (Amazon…