AWS and SoftwareOne collaborate on RISE with SAP
Duncan is an award-winning editor with more than 20 years experience in journalism. Having launched his…

Duncan is an award-winning editor with more than 20 years experience in journalism. Having launched his…

What Is Revenue Intelligence? Revenue intelligence is a data-driven approach that companies use to understand and…
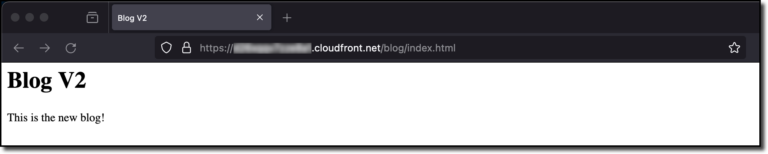
Amazon CloudFront allows you to securely deliver static and dynamic content with low latency and high…

Introduction Linux, an immensely powerful and versatile operating system, sits at the heart of countless applications,…

Ever thought of adding a playful twist to your content? Whether it’s for your social media…

It’s no secret that the cloud has changed the way business is conducted and operated –…

Last week I saw an astonishing 160+ new service launches. There were so many updates that…

Duncan is an award-winning editor with more than 20 years experience in journalism. Having launched his…

Duncan is an award-winning editor with more than 20 years experience in journalism. Having launched his…

In the constantly evolving landscape of technology, “AI is eating the world” has become more than…

I can’t believe it’s been 15 years since Amazon CloudFront was launched! When Amazon S3 became…

We are launching three new voices for Polly. Powered by a new long-form engine, the voices…
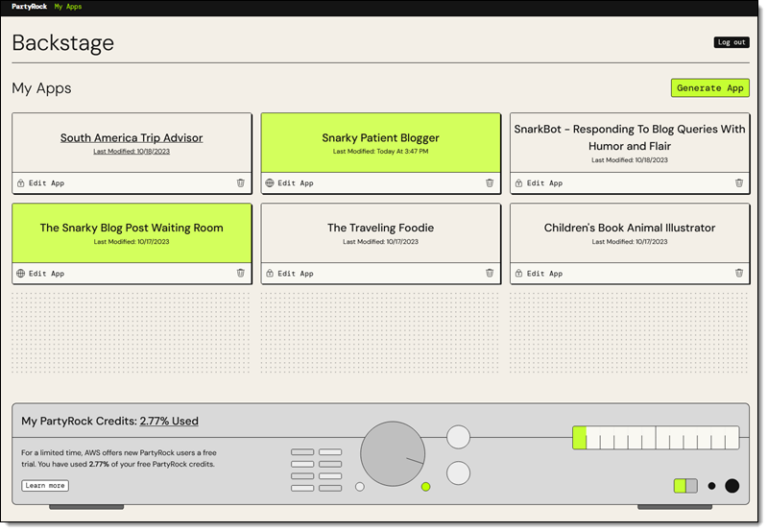
If you are ready to learn more about Generative AI while having fun and building cool…

Introduction Linux, the cornerstone of open source operating systems, has always been synonymous with flexibility and…

In the digitized corridors of modern healthcare, patient data emerges as the lifeblood, fueling every aspect…

About the Author By Duncan MacRae | 16th November 2023 Categories: Banking & Finance, Companies, Digital…
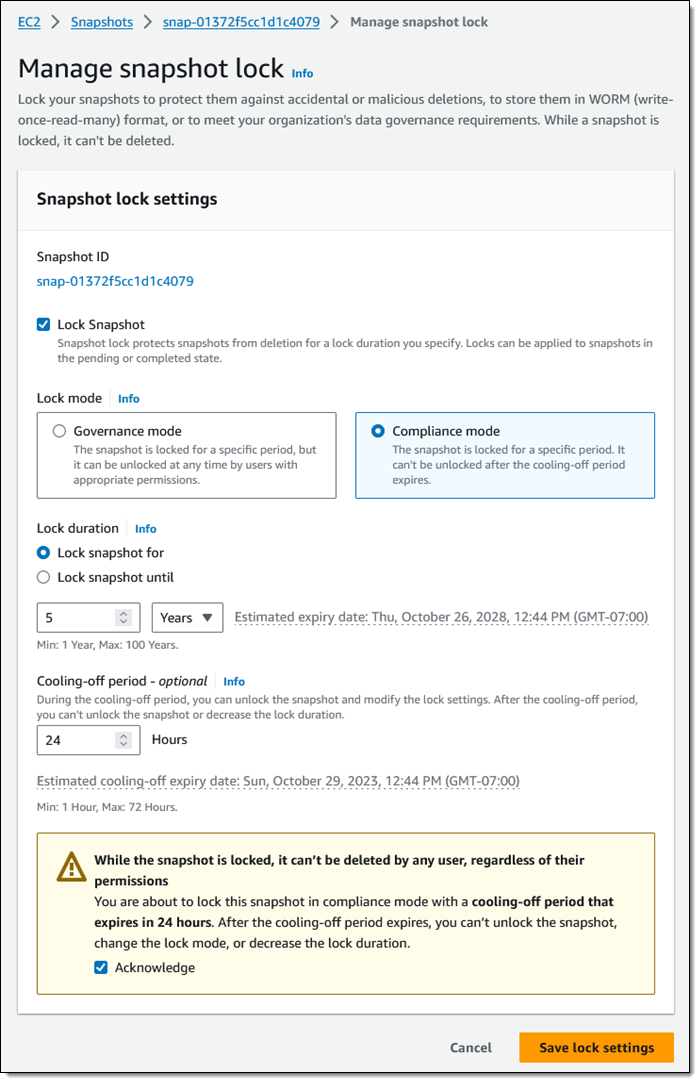
You can now lock individual Amazon Elastic Block Store (Amazon EBS) snapshots in order to enforce…

Cloud file storage is a method of storing data in the cloud rather than on local…